
WELCOME TO OUR WEBSITE
ACID Threat Intelligence
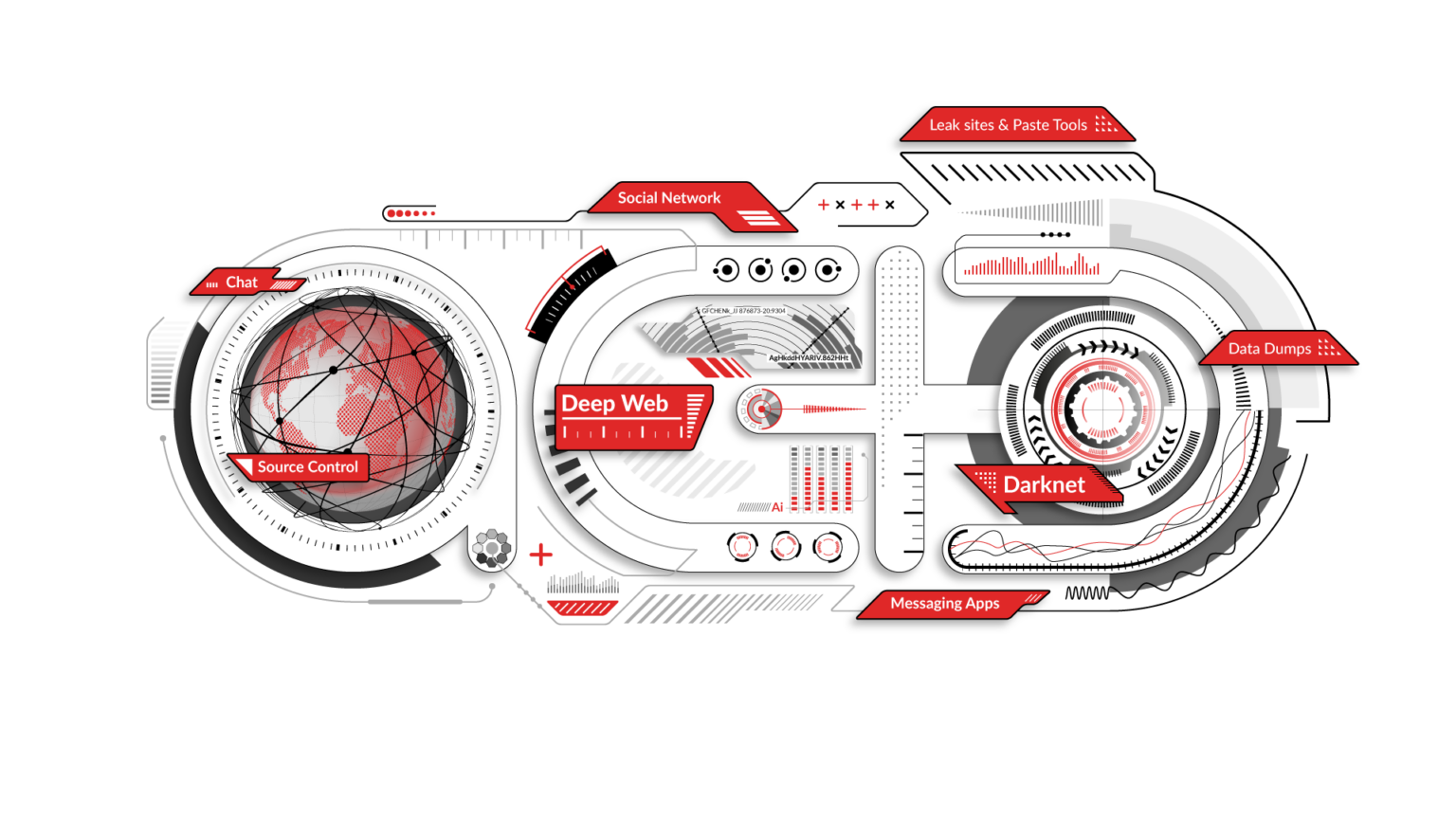
ACID is a dark web monitoring and cyber intelligence company that thoroughly scans the dark web and numerous other sources and platforms 24/7/365 to detect attacks as early as in their planning stage. Detailed real-time alerts enable you to implement effective countermeasures to foil the attacks or mitigate their consequences, support your business continuity and protect your reputation.
Cybercrime is continuing its upward trend, with the threat actors as bold and active as ever. In 2024, the average cost of a data breach in larger organizations reached a new high of $4.88 million. It is particularly concerning that breaches were identified an average of 194 days after they had occurred, yet the time elapsing from identification to containment was 292 days. However, many companies remain unprepared to deal with the threats – by some estimates, as many as 77% do not have a cybersecurity incident response plan. This leaves them facing heavy risks that could be disastrous to their business.
ACID Technologies is a well-established threat intelligence company, recognized for the high-quality services that it provides to companies and organizations operating in a wide variety of sectors and industries, including banking and finance, healthcare, education, transportation, energy, state and local government, gaming and gambling, and others.
We are rising to the challenge, to provide you with a cost-effective, individually tailored solution that enhances your cybersecurity posture without needing to expand your IT security workforce, in whichever industry or sector you operate. Our proprietary solution is based on 24/7/365 monitoring of the dark web and numerous other sources and platforms. The monitoring is meticulously tailored, based on client-specific keywords and relevant languages, in order to yield optimally precise results.
Our threat intelligence services alert you to the first hint of an attack targeting your organization, with all available information. The real-time actionable intelligence allows you to implement effective countermeasures to mitigate the consequences of the attack – be they disruption to operation, loss of business, payment of heavy regulatory fines, loss of clients, reputational damage, or other – and possibly foil it altogether.
ACID Technologies helps keep your organization safe, and supports it in maintaining its business continuity.
ACID INTELLIGENCE
ACID Intelligence performs 24/7/365 tailored monitoring of a broad range of sources by deploying clusters of robots and utilizing advanced AI algorithms. It also injects avatars and implements crawlers that imitate regular user activity to detect and counter threats before they materialize.
ACID provides advance warning of a looming hostile act in real time along with all available details, allowing you to shorten your TTM (time to mitigate), lessen the harmful effects of a cyber attack, or even foil it.
ACID Intelligence Benefits
Tailored threat detection
Keywords are defined individually for each client and are translated into multiple languages. The keywords can be easily amended, and new ones added as needed.
The intended target is provided with the most accurate and comprehensive details of an impending cyber attack. Additional information about the attack is provided as it becomes available, to enable optimizing the organization’s countermeasures, foiling it or minimizing the harm potentially arising from it.

Wide coverage
ACID continuously monitors a broad scope of sources and platforms for optimal threat detection: dark web; deep web; paste tools; dumpsites; leak sites; social media: Facebook, Twitter, Instagram, VK, Weibo; and chats: IRC webchat, Discord, Telegram, WhatsApp and WeChat.
ACID unleashes its clusters of robots and employs advanced AI algorithms to detect potential threats in emails and domain names, credit card data and banking information, cyber operations, intellectual property, key personnel, and much more.
When a wide array of cyber threat sources are continuously tracked, the risks of an attack by cybercriminals are greatly reduced.

Actionable advance alerts
ACID Intelligence provides you with detailed alerts at the first hint of a threat, which are generated by its cluster of robots that utilize performance-enhancing AI algorithms to comprehensively monitor a myriad of clear, dark, and deep web sources. These robots enable us to deliver the information you need to defeat the threat or minimize its impact.
The great advantage of this AI-enabled advanced alerting feature is that it enables you to be proactive in dealing with the threats that can penetrate your organization’s systems and hack into private accounts.
Real-time alerts
Alerts are displayed on a centralized dashboard immediately upon detection of any suspicious activity or direct threat, with all available information. As the perpetrators continue planning their attack, more data is collected, and the client organizaton is immediately notified of the newly acquired information. Updates are also sent in real-time by email and through the client’s SIEM system or can be retrieved via API.
Real-time alerts benefit the client organization by allowing it to optimize its response – implement the most effective tools to counter the threat, based on continuously updated, precise information, and fine-tune its response for maximum effectiveness.
Technological Compatibility and Security
ACID Intelligence:
• Is based on HTML5 CSS
• Supports UTF-8
• Comes with built-in integration for SIEM/SOAR via RESTful API
• Keywords can be defined in Regex
• Special templates are offered upon request
• Each ACID Intelligence client is allocated a private zone on the cloud for maximum security
ACID DIP
What is Digital Identity Protection?
The increasingly broad digital presence of governmental, public and private sector organizations, which has expanded to include social media and the ever-growing use of apps, exposes these companies and organizations to additional threats on many more fronts. These threats have the potential to cause severe financial impact on the companies, organizations and their clients, disrupt their operation, and harm their reputation.
ACID DIP helps keep companies and organizations safe through ongoing website, DNS, domains, apps and social media monitoring – all to ensure that their digital identity remains protected.
ACID DIP Modules
Website
DIP verifies the continuous availability of the organization’s website and immediately alerts if it is taken down or defaced by attackers. Concurrently, DIP also searches for offensive language or links to unauthorized sites.

DNS
DIP performs a DNS check to ensure that the organization’s clients are not rerouted from its website to a different IP address.
Domains
DIP checks for near-identical domains that aim to dupe clients; these may be distinguished from the client organization’s domain by as little as a single keyboard stroke. DIP thus prevents the organization’s need to buy numerous domains to protect itself and the associated financial cost: it can now buy only the domains it truly needs and monitor all the rest.
Additionally, DIP offers protection from phishing by searching for phishing sites that may deceive users and defraud them. To protect from phishing, ACID checks whether such a site has been launched, whether it includes the organization’s logo or text from the genuine site, and whether it requests user identification details.

Apps
DIP checks app stores for imposter apps, phishing apps, or apps similar to the organization’s, which cybercriminals and cyber terrorists can exploit to mislead and trick its customers. Importantly, DIP allows global organizations to monitor all their applications. While app stores (Google, Microsoft, Apple) differ between countries, DIP is equipped to alert to an attack taking place in one or more other regions, which has thus far gone unnoticed.

Social media
DIP monitors the organization’s social media presence on Facebook, Twitter, Instagram, VK, and Weibo, looking for tampering, and also checks for the presence of imposter accounts. It is important to note that even organizations with no social media presence can be attacked through imposter profiles.

Real-time alerts
Alerts of any hostile activity are immediately sent to the targeted organization’s contact persons via email and through the client’s SIEM system, or can be retrieved via API.
Technological Compatibility and Security
ACID DIP is based on HTML5 CSS.
It supports multi-language (UTF-8).
A keyword can be defined as Regex.
Built-in integration for SIEM/SOAR via RESTful API.
We also offer unique templates for your convenience.